Provider Lab Part 1
Let's create a lab with everything we need for our Crossplane study. The proposal is to create a lab with several providers of things we use in our daily work.
We'll reuse the Backstage lab and add Crossplane, but we'll add several extra providers to be able to explore different scenarios in the future.
We'll install using the values.yaml below.
Provider GitHub
Apply the yaml below.
apiVersion: pkg.crossplane.io/v1
kind: Provider
metadata:
name: provider-github
spec:
package: xpkg.upbound.io/coopnorge/provider-github:v0.13.0
Let's configure the GitHub provider using a personal token.
Let's create a secret containing inside credentials the token and owner which are the values it needs to fetch.
Create the github.yaml file
# github.yaml
apiVersion: v1
kind: Secret
metadata:
name: github-davidpuziol # Secret name, change to yours
namespace: crossplane-system
type: Opaque
stringData:
credentials: "{\"token\":\"${GITHUB_TOKEN}\",\"owner\":\"${GITHUB_ACCOUNT}\"}"
---
apiVersion: github.upbound.io/v1beta1
kind: ProviderConfig
metadata:
# This is a github provider config as we can see by the apiversion.
# A good practice is that by the name we can already know which account will be used
# Change to your account to make it easy.
name: github-provider-davidpuziol
spec:
credentials:
source: Secret
secretRef:
name: github-davidpuziol # Will reference the secret we created above.
namespace: crossplane-system
key: credentials
Each provider has its own Kind ProviderConfig which uses its own apiVersion.
We can have several provider configs for the same provider type. For example two different GitHub accounts.
Now let's apply what we have above.
export GITHUB_TOKEN="your-token"
export GITHUB_ACCOUNT="your-account"
# As yaml doesn't have the capability to substitute variables, we should do this before applying.
envsubst < gitlab.yaml | kubectl apply -f -
To test let's apply the manifest below to create a new repository.
apiVersion: repo.github.upbound.io/v1alpha1
kind: Repository
metadata:
name: test-repo-crossplane
namespace: default
spec:
forProvider:
name: test-repo-crossplane
description: "Test repository created via Crossplane"
visibility: "public"
hasIssues: true
hasWiki: true
autoInit: true
providerConfigRef:
name: github-provider-davidpuziol # See that we are using this provider config, so it goes to my account.
kubectl apply -f githubrepotest.yaml
repository.repo.github.upbound.io/test-repo-crossplane created
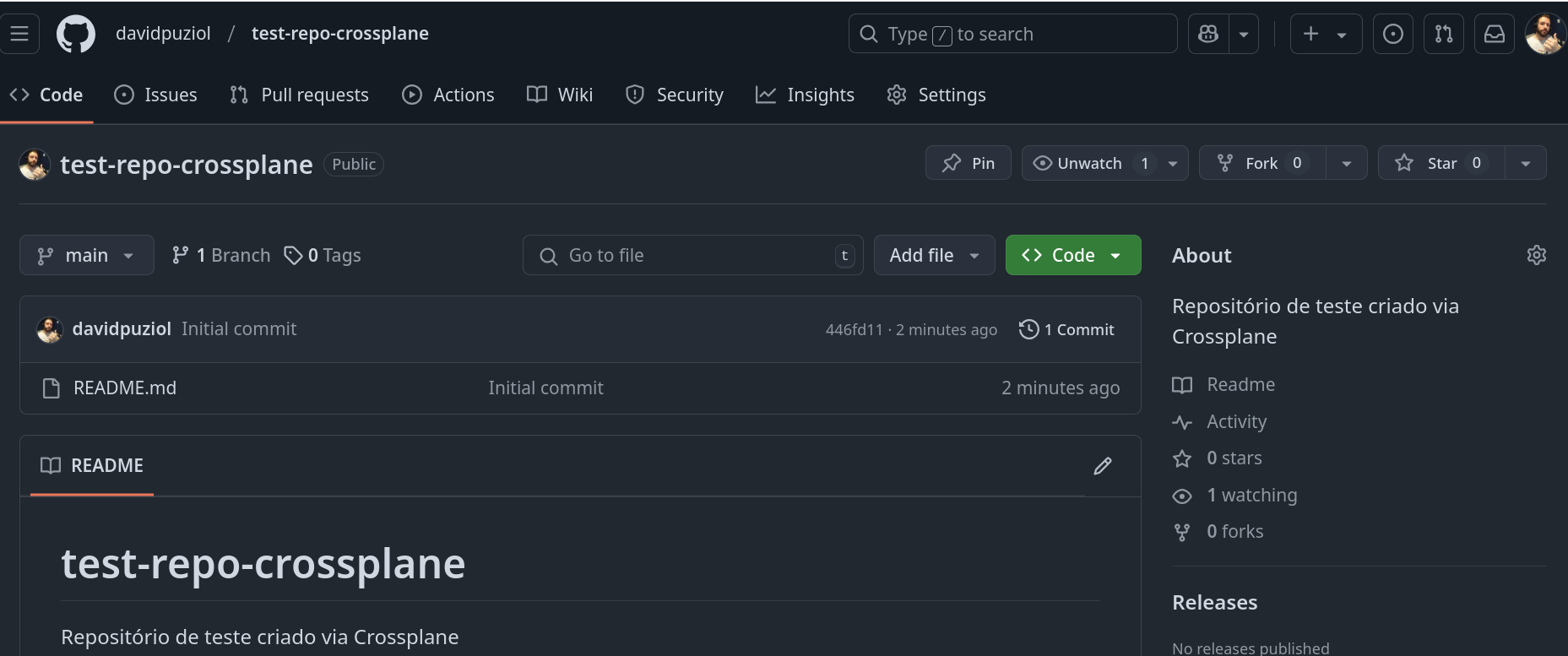
A curiosity is that this resource is cluster scope, meaning even though we defined the default namespace, it doesn't matter. Actually all GitHub custom resources are at cluster level.
❯ k get repositories.repo.github.upbound.io -n default
NAME SYNCED READY EXTERNAL-NAME AGE
test-repo-crossplane True True test-repo-crossplane 2m2s
❯ k get repositories.repo.github.upbound.io -n crossplane-system
NAME SYNCED READY EXTERNAL-NAME AGE
test-repo-crossplane True True test-repo-crossplane 2m15s
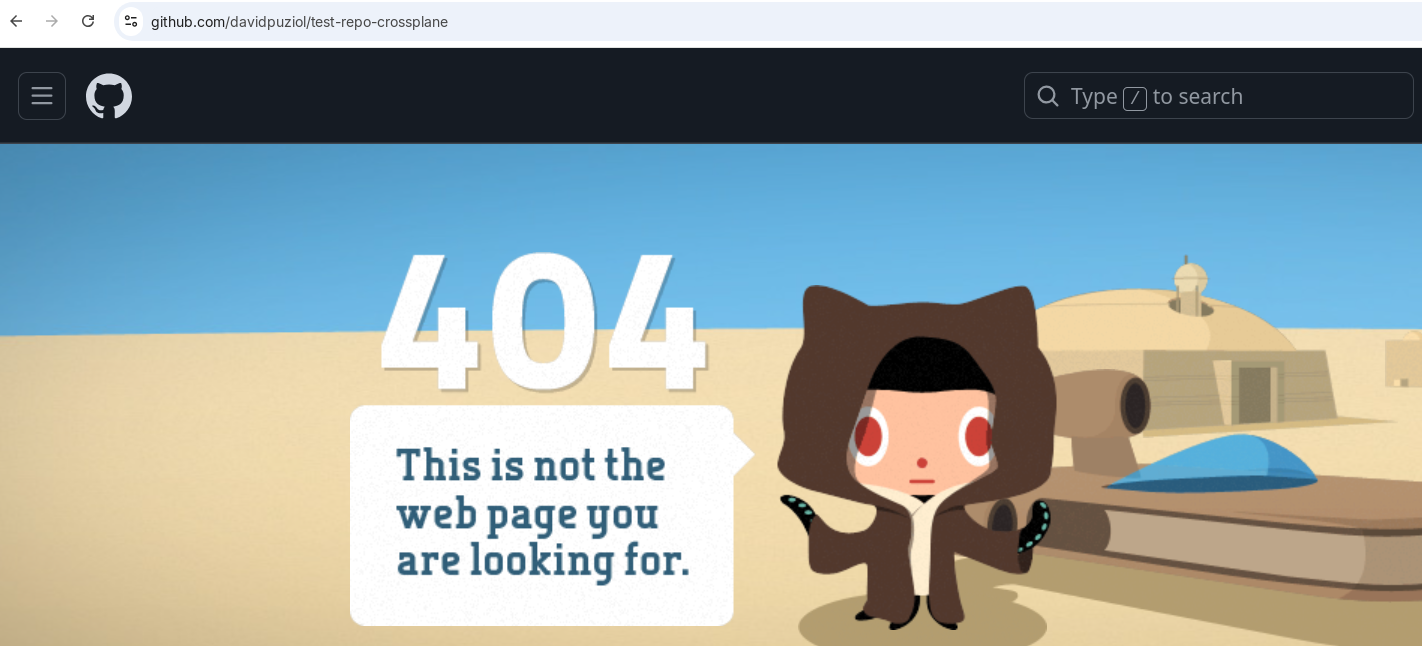
Deleting this resource.
kubectl delete repositories.repo.github.upbound.io test-repo-crossplane
repository.repo.github.upbound.io "test-repo-crossplane" deleted
Several new custom resources were created for GitHub use, despite us using repositories.repo.github.upbound.io.
k get customresourcedefinitions.apiextensions.k8s.io -n crossplane-system -o custom-columns=NAME:.metadata.name | grep github.upbound.io
actionssecrets.actions.github.upbound.io
actionsvariables.actions.github.upbound.io
branches.repo.github.upbound.io
branchprotections.repo.github.upbound.io
defaultbranches.repo.github.upbound.io
deploykeys.repo.github.upbound.io
emugroupmappings.team.github.upbound.io
memberships.user.github.upbound.io
organizationrulesets.enterprise.github.upbound.io
organizations.enterprise.github.upbound.io
providerconfigs.github.upbound.io
providerconfigusages.github.upbound.io
pullrequests.repo.github.upbound.io
repositories.repo.github.upbound.io
repositoryautolinkreferences.repo.github.upbound.io
repositoryfiles.repo.github.upbound.io
repositorywebhooks.repo.github.upbound.io
storeconfigs.github.upbound.io
teammemberships.team.github.upbound.io
teamrepositories.team.github.upbound.io
teams.team.github.upbound.io
teamsettings.team.github.upbound.io
teamsyncgroupmappings.team.github.upbound.io
Provider GitLab
We create the secret with the token we need.
apiVersion: v1
kind: Secret
metadata:
name: gitlab-davidpuziol
namespace: crossplane-system
type: Opaque
stringData:
token: "${GITLAB_TOKEN}"
---
apiVersion: gitlab.crossplane.io/v1beta1
kind: ProviderConfig ## Once again see that it's kind ProviderConfig for a different apiVersion.
metadata:
name: gitlab-provider-davidpuziol
namespace: crossplane-system
spec:
baseURL: https://gitlab.com/
credentials:
source: Secret
method: PersonalAccessToken
secretRef:
namespace: crossplane-system
name: gitlab-davidpuziol
key: token
And we have the custom resources below, all at cluster level too.
k get customresourcedefinitions.apiextensions.k8s.io -n crossplane-system -o custom-columns=NAME:.metadata.name | grep gitlab.crossplane.io
accesstokens.groups.gitlab.crossplane.io
accesstokens.projects.gitlab.crossplane.io
deploykeys.projects.gitlab.crossplane.io
deploytokens.groups.gitlab.crossplane.io
deploytokens.projects.gitlab.crossplane.io
groups.groups.gitlab.crossplane.io
hooks.projects.gitlab.crossplane.io
members.groups.gitlab.crossplane.io
members.projects.gitlab.crossplane.io
pipelineschedules.projects.gitlab.crossplane.io
projects.projects.gitlab.crossplane.io
providerconfigs.gitlab.crossplane.io
providerconfigusages.gitlab.crossplane.io
samlgrouplinks.groups.gitlab.crossplane.io
storeconfigs.gitlab.crossplane.io
variables.groups.gitlab.crossplane.io
variables.projects.gitlab.crossplane.io
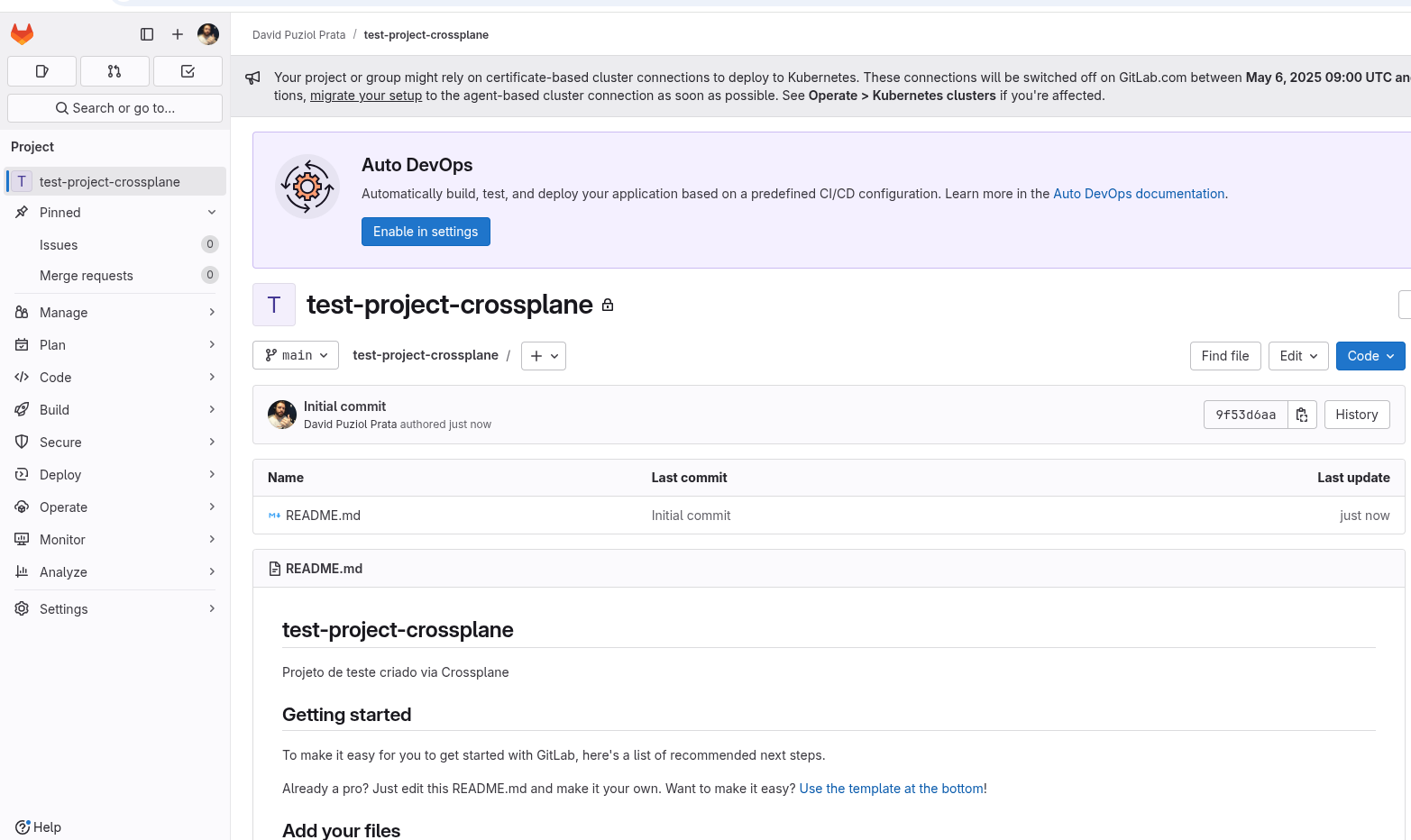
To create a repository it would be a different custom resource from GitHub. In GitLab we define a project.
apiVersion: projects.gitlab.crossplane.io/v1alpha1
kind: Project
metadata:
name: test-project-crossplane
namespace: default
spec:
forProvider:
name: test-project-crossplane
description: "Test project created via Crossplane"
visibility: private
initializeWithReadme: true
providerConfigRef:
name: gitlab-provider-davidpuziol
Applying this manifest we have.
kubectl apply -f /docs/iac/crossplane/resources/providers-configs/gitlabrepo.yaml
project.projects.gitlab.crossplane.io/test-project-crossplane created
k get projects.projects.gitlab.crossplane.io
NAME READY SYNCED AGE PATH WITH NAMESPACE
test-project-crossplane True True 23s davidpuziol/test-project-crossplane
To delete.
❯ k delete projects.projects.gitlab.crossplane.io test-project-crossplane
project.projects.gitlab.crossplane.io "test-project-crossplane" deleted