CIS Benchmark
CIS - Center for Internet Security is a non-profit organization dedicated to improving cybersecurity and resilience for organizations worldwide. Founded in 2000, CIS is widely recognized for its security best practices, frameworks, and benchmarks that help organizations protect their systems and data.
CIS is widely used by organizations of all sizes and sectors, including governments, businesses, and academic institutions, as a trusted source of guidelines and tools to improve cybersecurity. CIS recommended practices and benchmarks help organizations protect themselves against cyber threats, comply with regulatory requirements, and improve their overall security posture.
Main CIS Activities and Products
Developed through a unique consensus-based process, composed of cybersecurity professionals and subject matter experts worldwide.
-
CIS Controls: A set of recommended cybersecurity practices, organized in a list of priority actions that help mitigate the most common threats. These practices are frequently used as a guide for implementing effective security policies.
-
CIS Benchmarks: Globally recognized configuration standards for operating systems, software, and networks. The benchmarks provide detailed guidelines on how to configure systems securely, helping reduce vulnerabilities and increase system resilience against attacks.
-
CIS Hardened Images: Pre-configured virtual machine images, based on CIS Benchmarks, that are available on public cloud platforms such as AWS, Azure, and Google Cloud. These images are used to ensure VMs are configured with recommended security standards from the start.
-
CIS SecureSuite: A set of tools and resources that provides members access to benchmarks, security automation, and other tools that assist in implementing and maintaining security standards recommended by CIS.
-
Others...
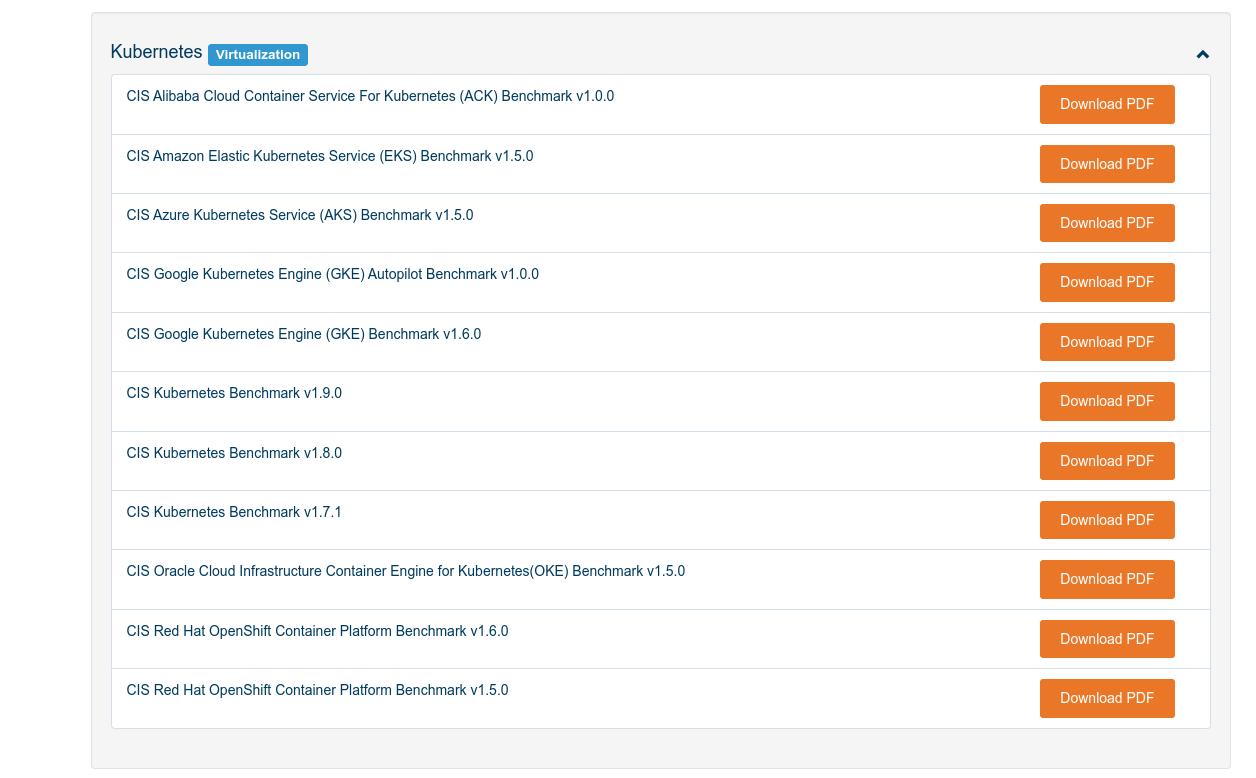
What interests us is the CIS Benchmarks for Kubernetes. Following all CIS guidance to have a secure cluster.
- They define standard security rules for Kubernetes. As administrators we can apply these rules, giving us a good security baseline. Kubernetes services offered by cloud providers already apply these rules, but make customizations.
If you don't want to register with CIS to download, I'll make the PDF available here to make it easier.
Note that we could download recommendations for major cloud providers, but since it's the CKS exam we'll use standard Kubernetes.
This is the latest version we have available for download, 1.9.0, and on page number 8 in Overview we see this document is valid for Kubernetes 1.27 to 1.29. Although we're on version 1.30, we don't have a better document to follow, so we'll use this one.
root@cks-master:~/default# k get nodes
NAME STATUS ROLES AGE VERSION
cks-master Ready control-plane 3d4h v1.30.3
cks-worker Ready <none> 3d4h v1.30.3
This document provides all the rules we need to make a cluster more secure, but it's not necessary for us to check the rules one by one. There certainly is some automation for this and that's what we'll do using kube-bench.
Get an overview of kube-bench.