CVEs: Common Vulnerabilities and Exposures

CVE (Common Vulnerabilities and Exposures) is a naming system used to identify and catalog known security vulnerabilities in software and hardware.
Each CVE is an entry in a list that is sponsored by CISA - Cybersecurity and Infrastructure Security Agency.
Why are CVEs important?
CVEs are important because they provide a universal standard for identifying and communicating security vulnerabilities. They help:
- Security Professionals: Quickly identify known vulnerabilities in systems and applications, enabling a faster and more effective response.
- Software Developers and Vendors: Track and fix security flaws in their products.
- Automated Security Tools: Correlate known vulnerabilities with systems in use, enabling more accurate security scans.
How is a CVE created?
- Discovery: A vulnerability is discovered by a security researcher, developer, or end user.
- Report: The vulnerability is reported to a CNA (CVE Numbering Authority), such as MITRE itself, software manufacturers, or security agencies.
- Assessment: The CNA evaluates the vulnerability, confirms its existence and impact, and then issues a CVE with a description.
- Publication: The CVE is added to MITRE's public database, where it's available to everyone and has the following structure:
- CVE ID: A unique identifier, such as CVE-2024-12345. This identifier consists of the prefix "CVE", followed by the year the vulnerability was discovered and a sequential number.
- Description: A brief summary of the vulnerability, including the potential impact and affected software or hardware.
- References: Links to additional details, such as security advisories, technical reports, or patches.
CVE Publication
There are several websites and databases that publish information about CVEs. Each of these sites may have a focus or specific set of information, complementing what is provided by MITRE and NVD (National Vulnerability Database) which are the two main ones for software development.
-
Focus Diversity: A different target audience or purpose. Some are more focused on giving context and additional technical details (like NVD), while others may focus on how to exploit vulnerabilities (like Exploit DB).
-
Disclosure Agility: Some sites are more conservative in publishing and prefer to wait to be sure of the vulnerability found, as it could be a false positive.
-
Sector or Product Specialization: Hardware and software vendors that publish vulnerabilities specific to their platforms.
Let's explore the main sites and their characteristics, with the first two being the most important for development:
-
MITRE CVE Database: Maintains the official CVE database, where all recognized vulnerabilities receive a unique identifier. This site is the primary source of CVE information and includes basic vulnerability descriptions. Provides a standardized list of CVE identifiers, with short descriptions for each vulnerability. Focused on standardization and ID assignment.
-
NVD (National Vulnerability Database): Maintained by NIST (National Institute of Standards and Technology) of the USA, the NVD is the official US government vulnerability database. It uses MITRE's CVE list as a base and adds details such as risk scores, CVSS (Common Vulnerability Scoring System) metrics, and information about impact, mitigation, and CVE categorization. Focus: Assigns severity scores (CVSS), provides additional technical details, links to patches and updates, and vulnerability categorization.
-
Exploit DB: An exploit database maintained by Offensive Security. This site is more focused on real exploits that use known vulnerabilities and can be used to test them. Focused on security researchers, red teams, and cybersecurity enthusiasts.
-
VulDB - Vulnerability Database: A vulnerability database maintained by a global community of security experts. Includes CVEs and other vulnerabilities not listed in official databases. Focused on fast and updated information, with features like vulnerability news feeds, statistics, and custom reports.
-
CERT (Computer Emergency Response Team) Websites: There are several CERTs around the world, such as US-CERT in the USA, JPCERT (Japan), and CERT-EU (European Union), which publish security alerts, including information about CVEs and guidance on how to mitigate specific vulnerabilities.
-
Manufacturer Security Advisories: Many manufacturers have their own security websites and publish information about vulnerabilities (CVEs) that affect their products and provide mitigation solutions, patches, and security updates.
-
Vulners Database: A vulnerability database that aggregates information from various sources, including CVEs, manufacturer security bulletins, and independent security reports to provide a broad view in a single location. Has free and paid versions, with the latter allowing expanded API access, personalized alerts, advanced search functionality, and support.
CVE Scanners?
There are several vulnerability scanners available that focus on detecting and analyzing CVEs in different environments (infrastructure, web applications, containers, clouds, etc.) with choices depending heavily on the project and budget.
-
Trivy: One of my favorites in the DevOps world for being open source. A lightweight and fast vulnerability scanner for containers, images, configuration files, and infrastructure as code (IaC) with focus on CVEs. The database is frequently updated. Very useful for pipelines.
-
Clair: A vulnerability scanner focused on containers, especially integrated with CoreOS and Kubernetes platforms. Analyzes container images to identify CVEs using vulnerability feeds from trusted sources to update the database.
-
Anchore: Security analysis and compliance tool for containers, widely used in pipelines.
-
Nessus: One of the vulnerability scanners with focus on CVEs, but not open source and extremely expensive. Detailed scans to identify CVEs in operating systems, applications, databases, and network devices (infrastructure in general). It's here to show that very robust solutions exist for this purpose, but generally used in really large companies with very critical systems.
-
OpenVAS (Greenbone Vulnerability Manager): An open source vulnerability scanner with focus on CVEs. Supports scanning systems and networks to detect known CVEs. -
Other scanners: Several others exist focused on specific language libraries like Retire.js for JavaScript libs andOWASPandSnykthat work for various languages. We also haveSnyk.
These scanners vary in terms of focus, from traditional infrastructure to container environments and modern applications. Choosing the right one depends on the context in which you want to scan for CVEs.
CVE Examples
-
CVE-2014-0160 (Heartbleed): A critical flaw in OpenSSL that allowed reading server memory, potentially exposing sensitive data, including passwords and private keys.
-
CVE-2017-0144 (EternalBlue): A security flaw in Microsoft's SMB protocol, exploited by the WannaCry ransomware.
-
CVE-2021-44228 (Log4Shell): A remote code execution vulnerability in Log4j, a Java logging library, that affected thousands of systems worldwide.
CISA
Created to improve cybersecurity, protect critical infrastructure, and coordinate responses to cybersecurity incidents in the United States, but goes beyond cybersecurity.
CISA performs several important functions to ensure the cybersecurity and physical security of the United States:
-
Critical Infrastructure Protection: energy, transportation, water, communications, finance, health, and others that are essential for the functioning of society and the economy.
-
Cybersecurity: Coordinates efforts to prevent, mitigate, and respond to cyber threats, for both government entities and the private sector. Provides guidelines, alerts, and best practices to help protect networks and systems against cyber attacks.
-
Incident Response: Helps government and private companies investigate cyber attacks and develop response and recovery strategies.
-
Vulnerability and Threat Disclosure: Publishes security reports, discloses information about known vulnerabilities (including CVEs), and issues security alerts about emerging threats. Works with other entities, such as MITRE, to share vulnerability information.
-
Training and Technical Assistance: Offers training, workshops, and simulation exercises.
CVSS (Common Vulnerability Scoring System)
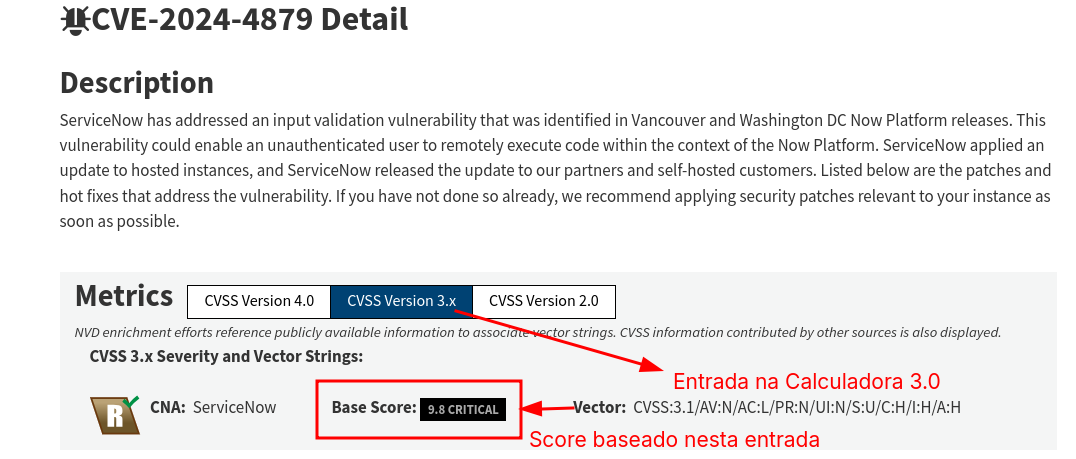
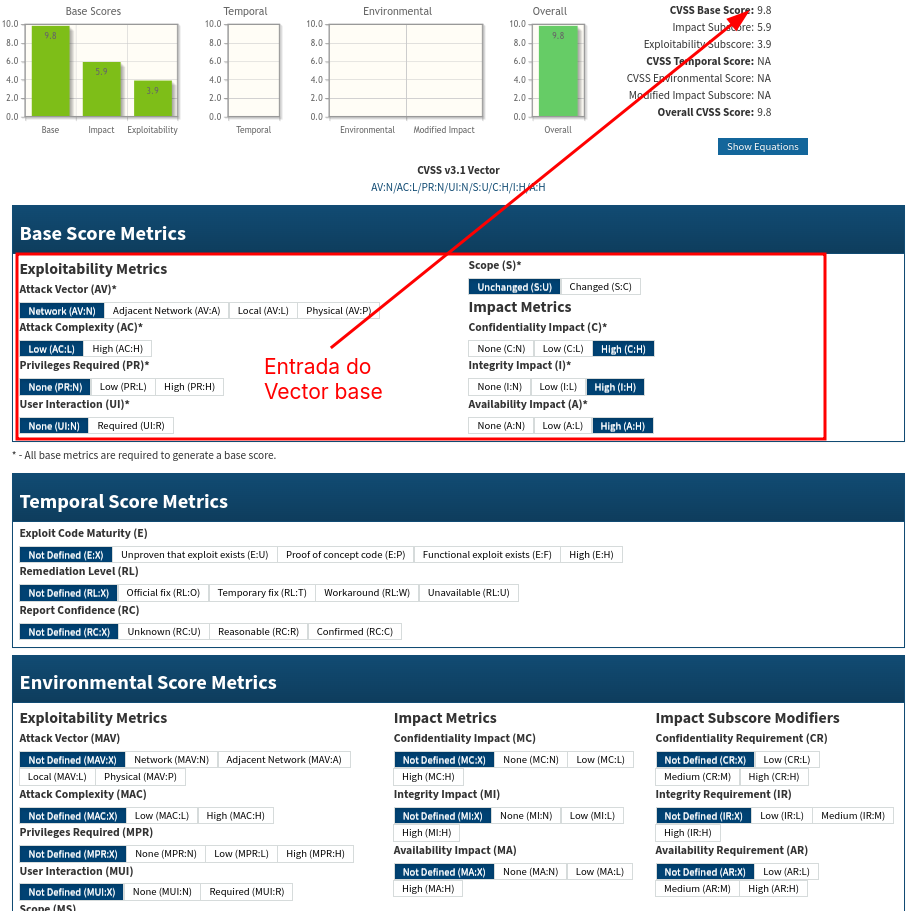
Generally NIST initially calculates the score of a CVE for a general purpose (base), but this score may not reflect the application environment scenario. So it's possible to rebalance the weights (vector) applied to the CVE.
Start with the weights found in NIST and redo the calculations and see how severe the CVE really is for another scenario.
We already have the 4.0 calculator but the vector doesn't always appear for it.
Calculators:
Now let's rebalance. I selected some random values, obviously we shouldn't take them into consideration and it's just for sampling.
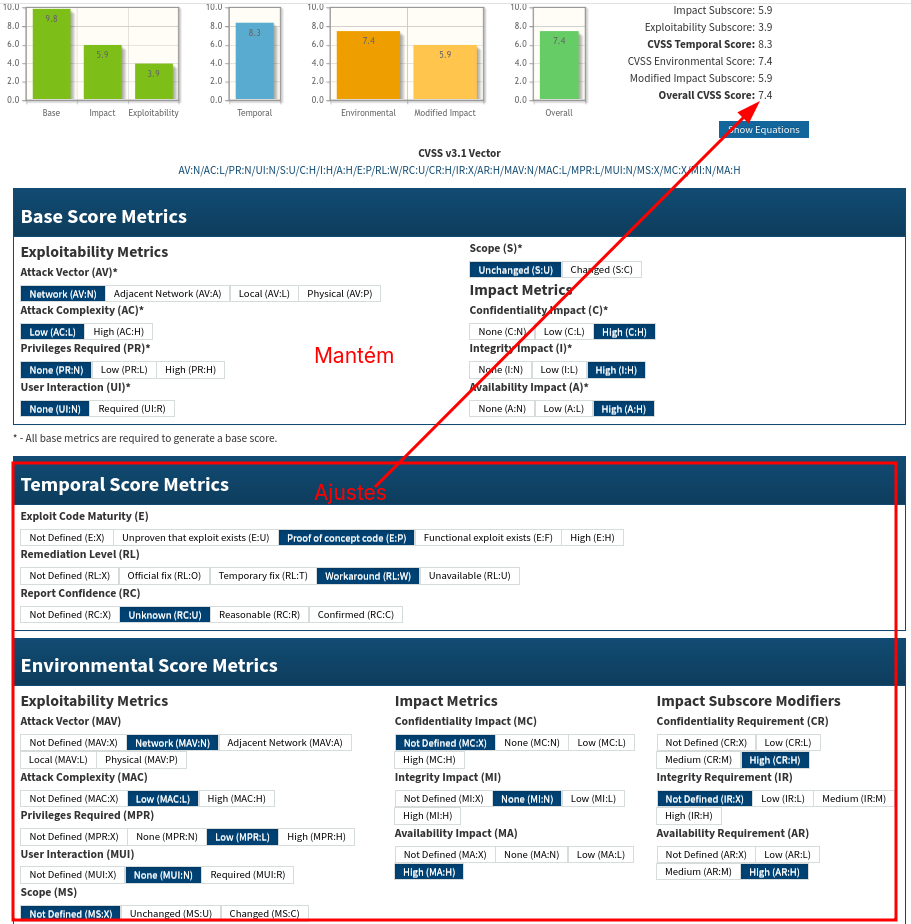
Read the CVSS standards guide to fully understand how to assess vulnerabilities using CVSS and interpret the resulting scores. Scores are computed in sequence, so that the Base Score is used to calculate the Temporal Score and the Temporal Score is used to calculate the Environment Score.