Security Primitives
In a production Kubernetes cluster, security is the main concern.
Naturally, all access to hosts must be protected.
- Disable root access.
- Disable password authentication access.
- Only allow access via SSH key.
- Other precautions such as physical and virtual access to the infrastructure hosting Kubernetes.
If something is compromised, everything is compromised
The kube-apiserver is at the center of all Kubernetes communication, being the communication between Kubernetes components and the user themselves using kubectl. Through it we can do anything in Kubernetes, so the first line of defense is controlling access to the kube-apiserver.
We need to ask ourselves...
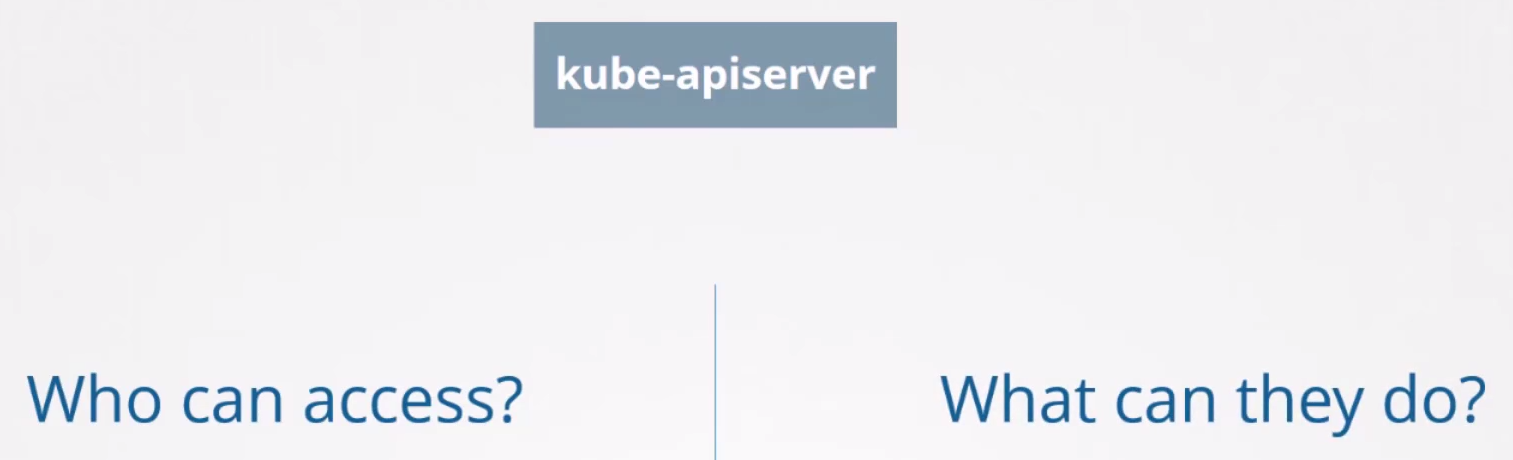
Who can access can be defined by different authentication methods.
Username and tokensstored in files.Certificates.- External authentication providers -
LDAP. Service Accountsfor machines.
Once access is allowed, what can be done? Various mechanisms will be studied here.
- RBAC Authorization
- ABAC Authorization
- Node Authorization
- Webhook Mode
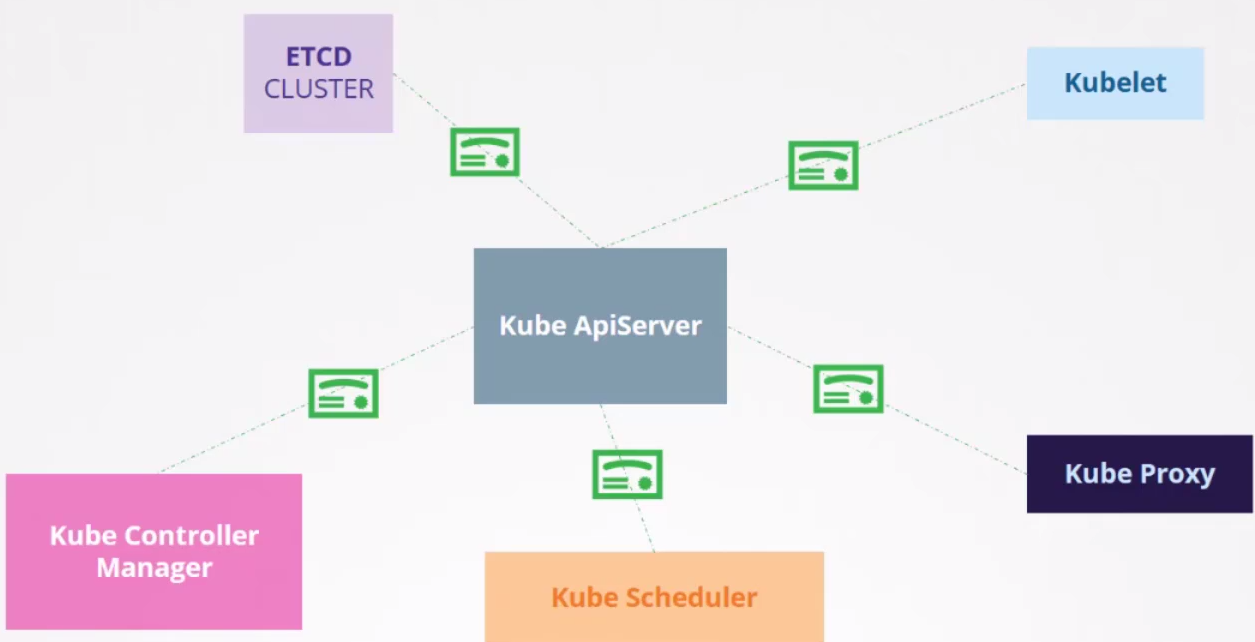
All communication between Kubernetes components is encrypted by TLS.
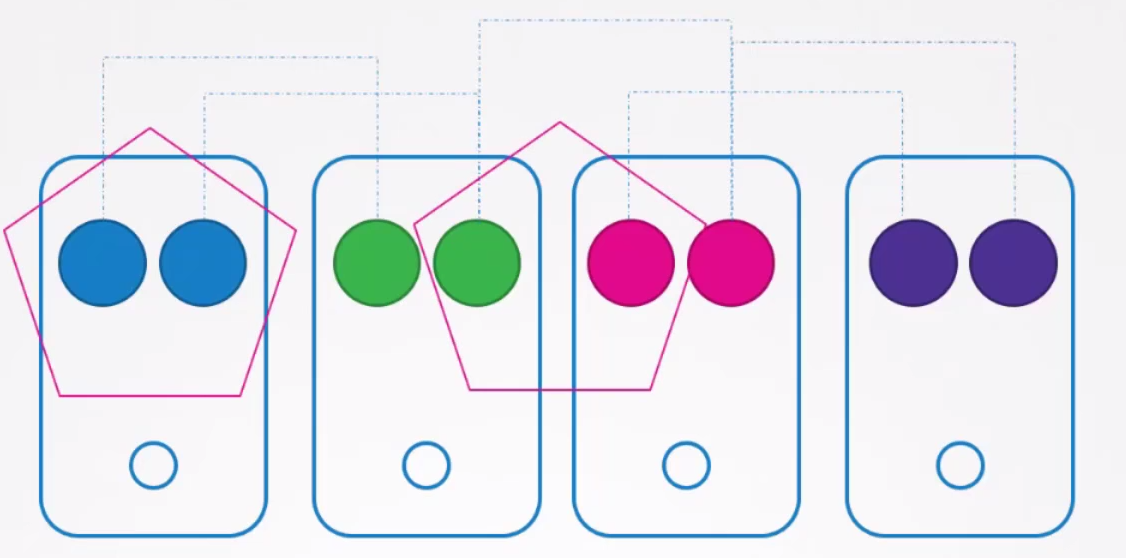
By default all pods can access all pods within the cluster and to restrict these accesses we can use network policies.