Images Vulnerabilities
To understand, you need to know what CVEs are.
One of the most common examples of vulnerability is buffer overflow. Imagine we have an Apache server running in a version that allows this exploit. We can send a specific request to this server and instead of just serving HTML, it can execute a script on the server.
Exploitis a term used in information security to describe a technique or software designed to take advantage of a specific vulnerability in a system, application, or network. The main objective of an exploit is to exploit this vulnerability to obtain unauthorized access, execute malicious code, or cause some other harmful effect.
In the case of Kubernetes, the targets are:
- Remotely accessible applications in containers
- Local applications within containers.
Vulnerabilities are not only from the applications we're interested in running; they're an inheritance from the base image used and everything we install from it, including libraries. For example, if we're running a container with our application and we're using the Ubuntu base image and it has some vulnerability, then we'll inherit it.
As a result, we may have vulnerabilities of:
- Privilege escalation
- Information disclosure
- DDOS
- etcd
We need a tool that can help scan all binaries and their dependencies in all container layers.
We can discover vulnerabilities during: the image build process or by checking at runtime the containers running in pods. Obviously it's better to find problems before the pod is running in the cluster.
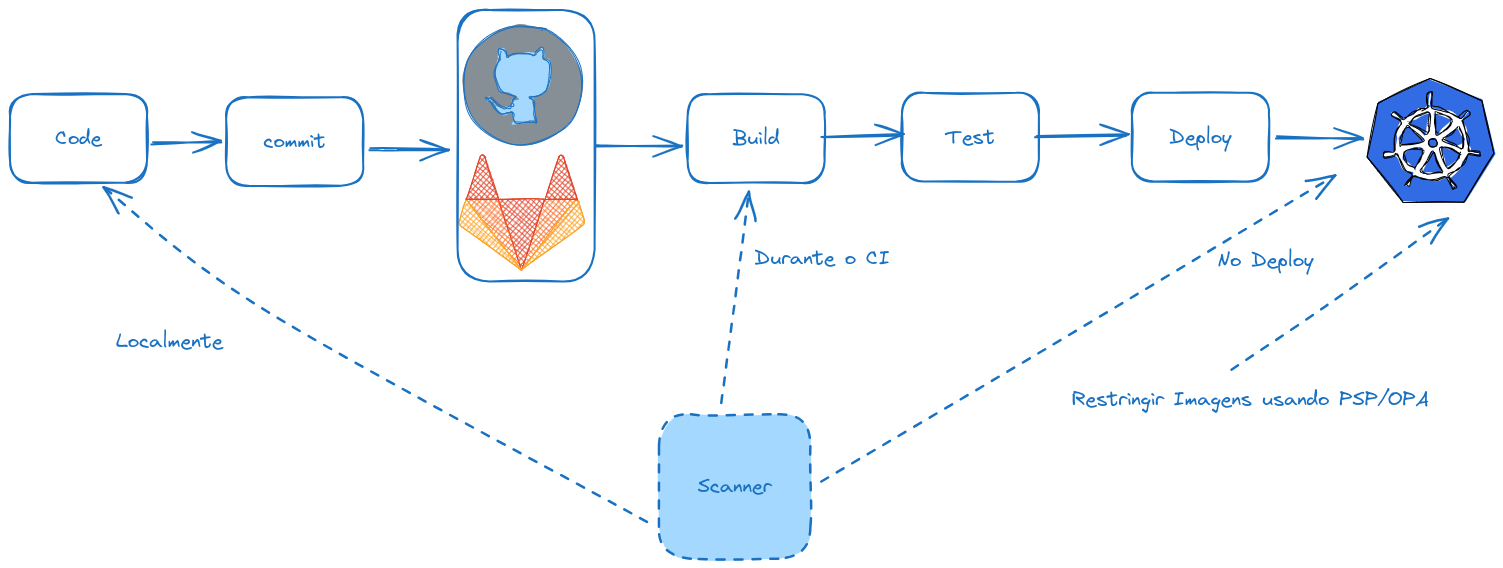
Two widely used open-source tools are Trivy and Clair. Study especially Trivy which is easier to use.
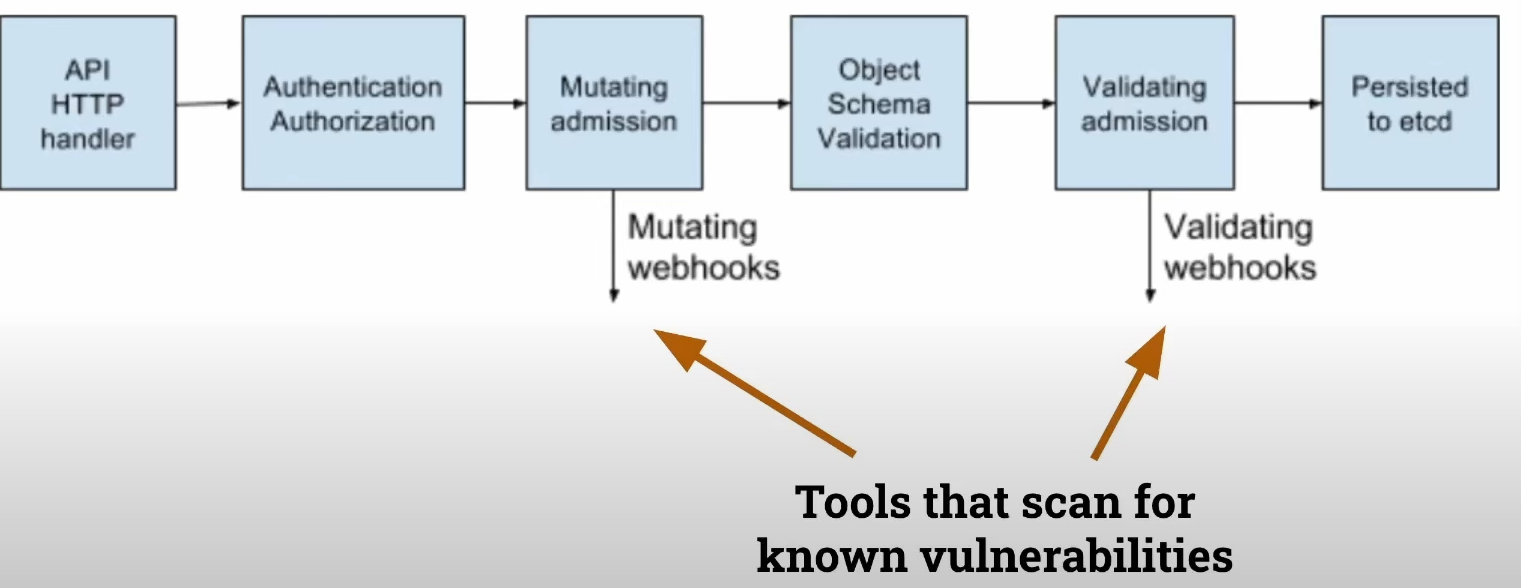
We can use the admission controller along with OPA or PSP to restrict repositories/images or make changes to requests. If an image uses a previous layer that's restricted, it won't be able to be executed because pulling that layer won't be allowed. If we make a change for example from ubuntu:20.04 to ubuntu:22.04 to fix, we can use the mutation webhook for this.