Architecture and Concepts
If we think about a typical large company, it's usually divided into departments that can contain one or more teams. Each team implements software (microservices) in various different languages and can use different clouds or even run on-premise. The technology used is not so important, but how they will manage the users of their applications is. What will be the authentication and authorization method? How will users be divided by groups and roles?
Certainly we don't expect applications to manage them on their own, especially for security reasons.
These users can be internal, external from partner companies, or can even be users from social applications (Google, Apple, Facebook), etc.
These applications need help to manage their users in the most secure way possible, this is where identity and access management comes in, in our case Keycloak.
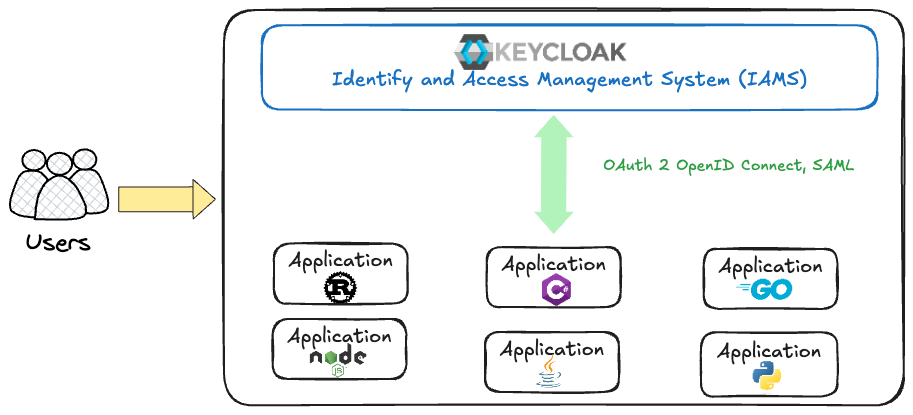
Keycloak allows configuring various authentication and identity federation protocols, such as OpenID Connect, OAuth 2.0, SAML 2.0, LDAP, among others, so that applications can integrate with it securely.
What Keycloak offers us is a central location where all identities can be managed and this is extremely important in a company where security is fundamental.
Normally, a company would have requirements like removing this user from an application, removing them from a group in that application, removing them completely from the organization, periodic key and token rotation, etc. With an IAMS we can do this centrally by the administrator.
Keycloak can be used as a single sign-on server (SSO - Single Sign On). Basically, it can act as a SAML identity provider or can even act as an OAuth authorization server. So, as mentioned earlier, your applications can use SAML or OpenID Connect to do single sign-on in your company.
It can act as an identity broker in the middle between your application and another identity provider, whether from partners or Social Providers.
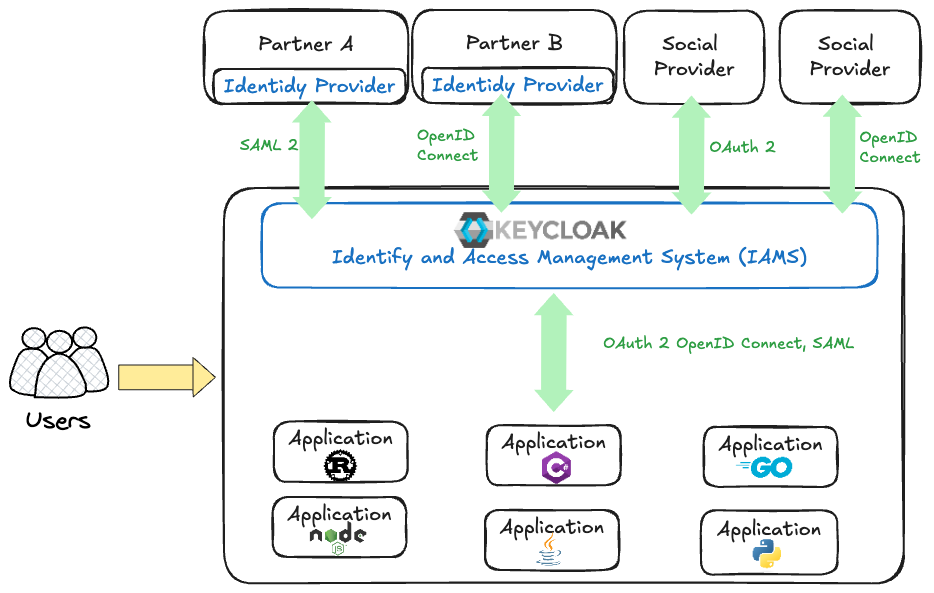
Basically, applications deployed in our company may need to have users from these partner organizations. The safest way to do this is to leverage their identities stored in their own identity providers. In this case, Keycloak can communicate with these identity providers using SAML or OpenID Connect.
We may want Internet users who are basically Google or Facebook users. Maybe we want them to access our application. Keycloak can also communicate with them using OAuth or OpenID Connect.
Keycloak can also connect to existing LDAP servers, such as Active Directory or Novell NetWare, to pull all users from directory servers into Keycloak.
So if we think about this at a higher level, Keycloak can consolidate all these users from different identity providers and manage them centrally, even though some of them are not actually defined in Keycloak itself.
Keycloak also provides multi-factor authentication for users immediately.