Realm
The first thing we can observe is the concept of Realms.
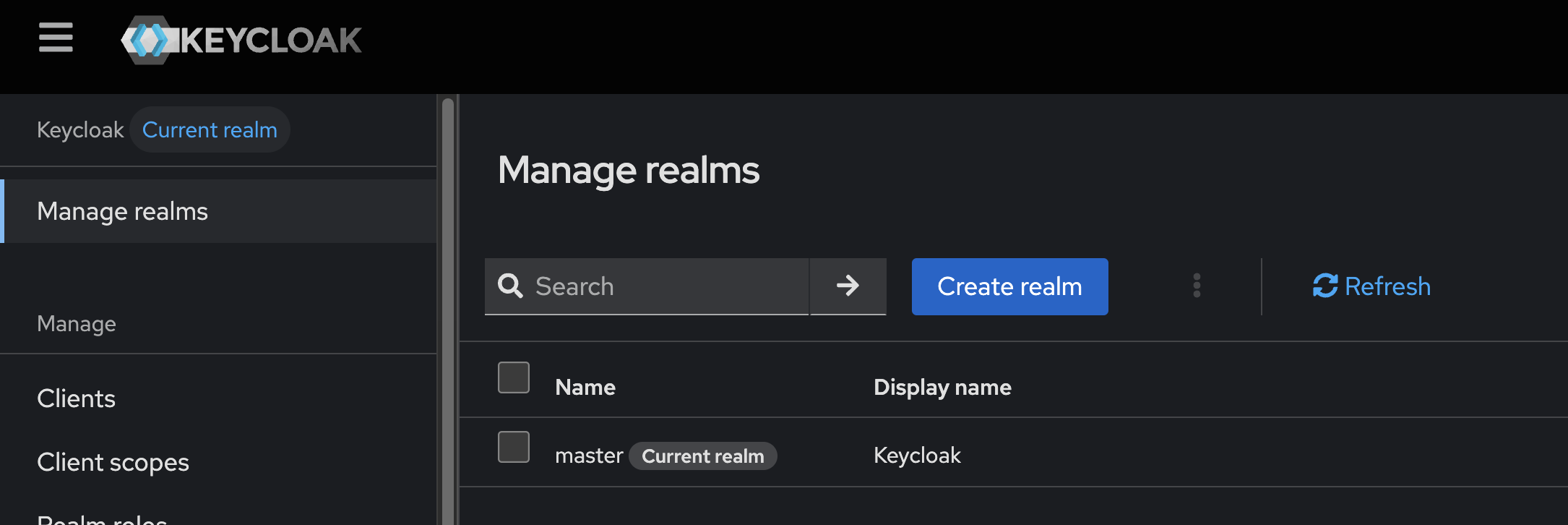
To understand what a realm is we need to keep in mind that Keycloak works with the concept of multi-tenant. Each tenant is like an instance of keycloak intended for an organization. Users, groups, applications, etc., are organized into realms. A company can have a single realm for everything or several realms, it depends on how they prefer to organize things. Whether to segregate or not segregate, whether by department, by squad, by type of application, by product, etc., is a question of architecture and each realm can be managed separately by its own administrators.
The master realm is special, used to administer Keycloak itself. A master realm administrator can also configure other realms.
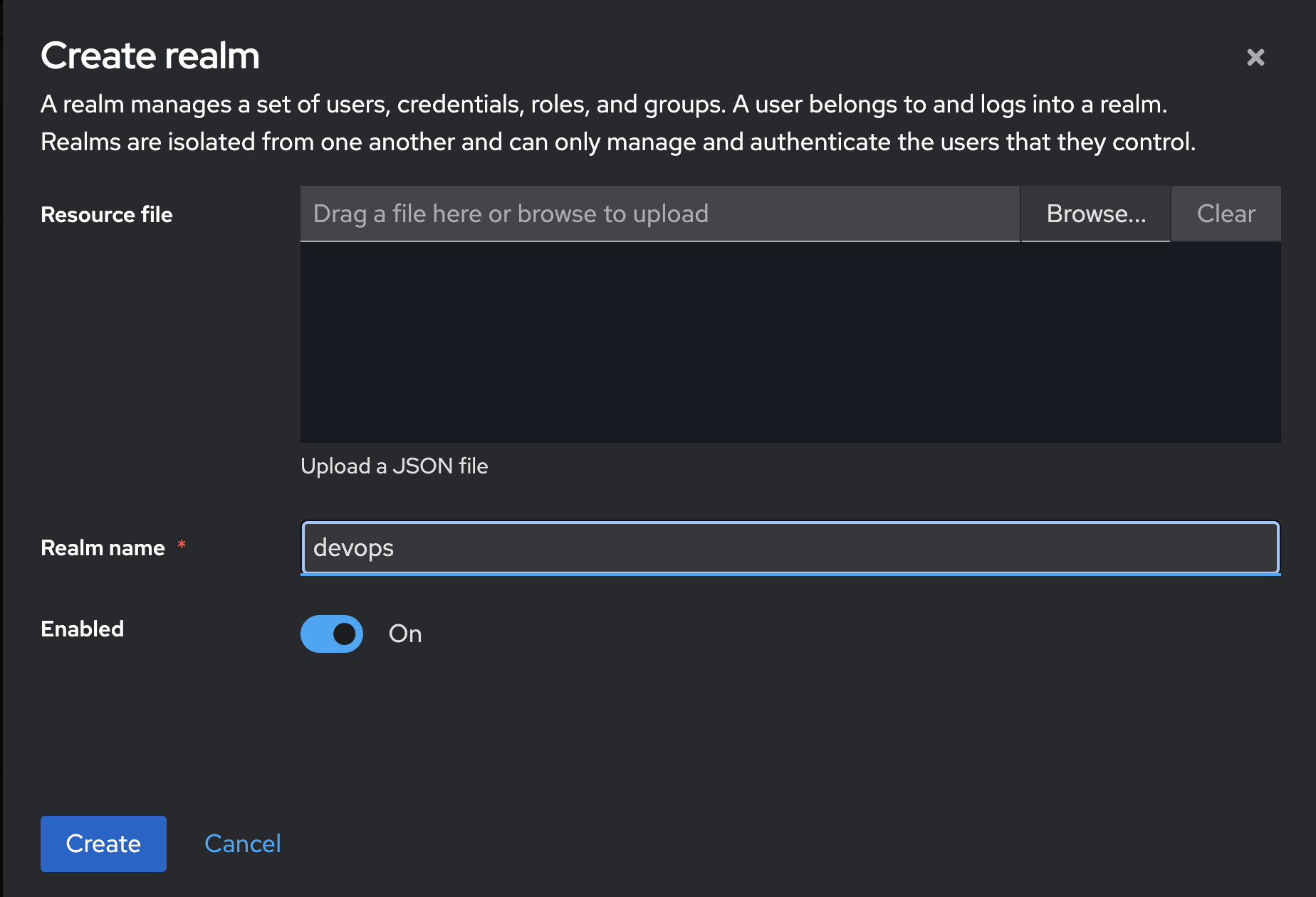
Let's create our first realm. I'll call it devops.
It's totally possible to use one Keycloak realm as an identity provider for another realm within the same Keycloak. This approach is known as internal Identity Brokering. This integration still requires manual configuration, as if they were two distinct systems.
When we start a realm we also start an OAuth2 authorization server and the SAML Identity provider. By accessing Realm Settings>General of this realm we have two links below for configuring the OpenID and SAML endpoint.
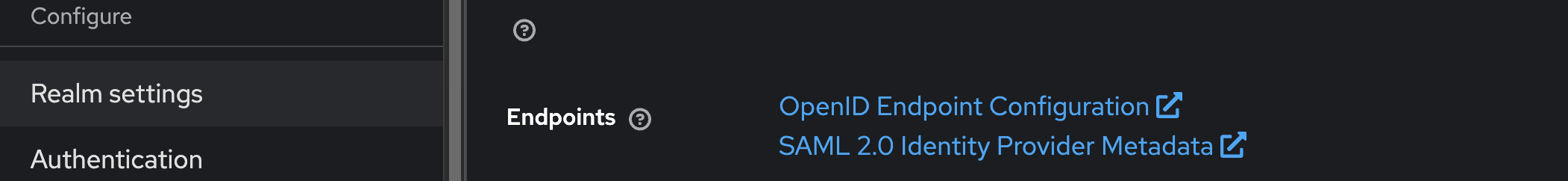
OpenID Endpoint Configuration: It's a JSON that automatically exposes all the important URLs and configurations of the devops realm for OIDC (OpenID Connect) clients to be able to integrate with Keycloak without needing to configure everything manually. It serves so that applications (OIDC clients) dynamically discover:
- Authentication endpoints
- Token endpoints
- Logout endpoints
- JWKS endpoints (signature public keys)
- Supported scopes, claims, grant types, etc
This link is actually https://keycloak.puziol.com.br/realms/devops/.well-known/openid-configuration and is intended to be public and doesn't expose any sensitive information, it just serves as an information of:
{
"issuer": "https://keycloak.puziol.com.br/realms/devops",
"authorization_endpoint": "https://keycloak.puziol.com.br/realms/devops/protocol/openid-connect/auth",
"token_endpoint": "https://keycloak.puziol.com.br/realms/devops/protocol/openid-connect/token",
"userinfo_endpoint": "https://keycloak.puziol.com.br/realms/devops/protocol/openid-connect/userinfo",
"jwks_uri": "https://keycloak.puziol.com.br/realms/devops/protocol/openid-connect/certs",
...
}
Who uses this? Web/mobile applications that authenticate via OIDC, libraries (passport.js, Spring Security, Dex, etc), Keycloak itself (when configuring identity brokering with another IdP), etc. With this we know exactly what messages should be sent to these endpoints to obtain the token.
Making an analogy,
.well-known/openid-configurationis to OpenID whatswagger.jsonis to a REST API.
In the case of the link SAML 2.0 Identity Provider Metadata it describes in XML the keycloak IdP provider in this realm for use with SAML 2.0. It's used by Service Providers (SP) to automatically configure trust with Keycloak.
This XML includes:
- entityID: unique identifier of the IdP
- URLs of:
- Single Sign-On (SSO)
- Single Logout (SLO)
- Binding information (HTTP-Redirect, POST, etc)
- Public certificates used to sign responses/assertions
Our xml
<!-- -->
<md:IDPSSODescriptor WantAuthnRequestsSigned="true" protocolSupportEnumeration="urn:oasis:names:tc:SAML:2.0:protocol">
<md:KeyDescriptor use="signing">
<ds:KeyInfo>
<ds:KeyName>DDLZ-ZDCmQddCrDNfaPcwxiJOdKsZLWExxkajG0bBjo</ds:KeyName>
<ds:X509Data>
<ds:X509Certificate>MIICmzCCAYMCBgGW+n640TANBgkqhkiG9w0BAQsFADARMQ8wDQYDVQQDDAZkZXZvcHMwHhcNMjUwNTIzMDAxMzUxWhcNMzUwNTIzMDAxNTMxWjARMQ8wDQYDVQQDDAZkZXZvcHMwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEKAoIBAQC74T6+gdPNOYl7RTRFU6rid/ofj13RbI9ZtfmlykR1qXNoIiT+ndy/14BFsRDJIY7dEOa7SOJUiR77M4LslAPYaIhszZ6RRuJ4u+WW5UQpZ8BLtaG7B4c5k/EHPkBfVitQUnj4Ss0gM53fkBIWg6b1A9eM6BRdawpTxXb0o2v4z6wsEOzbrHrbsz7DHOB792/tqzd+gIo35oAg9mGtI5s3Cu2SyoPJZg9YY2Q2cCRXA+auZ+rYEAAGIeLdO7s+/qJ3dblVy/3D08ZSvExoFuY2/3lzEzqp6b0XmBwwqGIHdWwX61+s4ZarrXdWR/km5Z6dueZbt03wchG3qexWrK3XAgMBAAEwDQYJKoZIhvcNAQELBQADggEBAFt/VbuSqp2mBmW28BFJ9HACU+Idd37TBnTuUJERAgAZHoRrbRVtBUd1Harc2Xn7ZfbNno+AiHbeg+rzEf3Spa9qqUGW5PIvCLtvxFec/d/VatF5EHndi8ReEIqz6vgQdagjt6m61rywj30FoQanbimnTsJxjCp/03pZxx/0F7+Q+gR7TWbq+SAxqlL6DPz+a6uDjrfcmRKCFrX3oNl6j5/yJ4JJGzhx3+AKxzyidw5YP8+EuRwerXpUtXDV/gQCF5hnLAEA4lDRLtOqqrMSgpJ34m/+IZfx69WEvPtu3KMcL8DkBUmFj8lxcQPb7Sdu2ZMCRKd3r2WEK/mGYlgBwzE=</ds:X509Certificate>
<!-- -->
<md:ArtifactResolutionService Binding="urn:oasis:names:tc:SAML:2.0:bindings:SOAP" Location="https://keycloak.puziol.com.br/realms/devops/protocol/saml/resolve" index="0"/>
<md:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="https://keycloak.puziol.com.br/realms/devops/protocol/saml"/>
<md:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="https://keycloak.puziol.com.br/realms/devops/protocol/saml"/>
<md:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Artifact" Location="https://keycloak.puziol.com.br/realms/devops/protocol/saml"/>
<md:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:SOAP" Location="https://keycloak.puziol.com.br/realms/devops/protocol/saml"/>
<md:NameIDFormat>urn:oasis:names:tc:SAML:2.0:nameid-format:persistent</md:NameIDFormat>
<md:NameIDFormat>urn:oasis:names:tc:SAML:2.0:nameid-format:transient</md:NameIDFormat>
<md:NameIDFormat>urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified</md:NameIDFormat>
<md:NameIDFormat>urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress</md:NameIDFormat>
<md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="https://keycloak.puziol.com.br/realms/devops/protocol/saml"/>
<md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="https://keycloak.puziol.com.br/realms/devops/protocol/saml"/>
<md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:SOAP" Location="https://keycloak.puziol.com.br/realms/devops/protocol/saml"/>
<md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Artifact" Location="https://keycloak.puziol.com.br/realms/devops/protocol/saml"/>
</md:IDPSSODescriptor>
</md:EntityDescriptor>
Creating another realm we have other endpoints for both OpenID and SAML. The links are the same, only the realm would change.
https://keycloak.puziol.com.br/realms/otherrealm/.well-known/openid-configurationhttps://keycloak.puziol.com.br/realms/otherrealm/protocol/saml/descriptor
But is the certificate the same in the case of SAML? No. It would be a completely different certificate. Do your test.
To better understand what we're going to talk about from here on, I recommend the readings: