The Color Wheel in Information Security Teams
The Security Team Color Wheel is a conceptual framework used in information security to categorize different functions, responsibilities, and approaches within an organizational security structure.
It all started simple with only two teams, one for attack (Red) and one for defense (Blue). Later, the security team focused on software development (Yellow) emerged. However, with the vast field of security specializations, it was necessary to expand by including a broader range of "colors," each representing a specific function in the cybersecurity ecosystem.
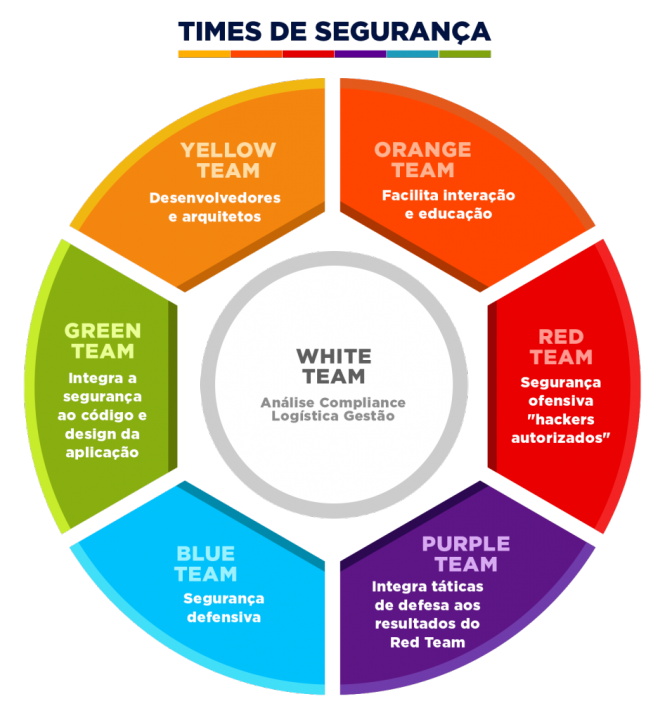
In this second expansion phase, we'll see that the formed colors are mixtures between primary colors.
The vast majority of companies don't have a formal structure for all these "colored teams" in security. In practice, it's common for some people to accumulate different functions, wearing "multiple hats" as needed, especially in smaller security teams.
Red Team
The Red Team simulates attacks against the organization's systems and infrastructures, adopting the mindset and tactics of real adversaries. Its goal is to identify vulnerabilities before malicious attackers can exploit them.
- Offensive security
- Social engineering
- Ethical hacking
- Perform penetration testing (pentest)
- Simulate advanced persistent threats (APTs)
- Assess the effectiveness of existing security controls
- Provide constructive feedback to improve defenses
Blue Team
The Blue Team is responsible for defending the organization's systems and networks, done proactively. While the Red Team tries to find flaws, the Blue Team works to actively protect digital assets.
- Monitor networks and systems for suspicious activities
- Respond to security incidents
- Implement and manage security tools
- Develop and maintain security policies
- Analyze logs and security alerts
Yellow Team

The Yellow Team is responsible for building and maintaining security in software development (where developers work), focusing on security architecture and systems design. The Yellow Team has the responsibility to develop applications with the Shift Left concept, where secure coding should be foreseen from software architecture to its completion, reducing rework and costs with late security review in code.
- Design robust security architectures
- Implement security by design principles
- Develop secure configuration standards
- Evaluate new technologies from a security perspective
- Create resilient and secure environments
Application developers, software engineers, and architects fall into this category.
Purple Team

Red + Blue = Purple
The Purple Team represents the integration between red and blue teams, promoting collaboration instead of competition. Its goal is to maximize organizational learning through the combination of offensive and defensive skills.
- Facilitate communication between red and blue teams
- Ensure lessons learned in attack exercises are incorporated into defenses
- Develop collaborative security exercises
- Implement a continuous security improvement cycle
- Improve detection and defense capabilities
In the Purple Team are the technical managers of the Blue and Red teams.
Green Team

Blue + Yellow = Green
The Green Team focuses on secure software and application development. They integrate security practices into the development cycle from the beginning.
The Blue Team isn't always aware of all structures, libraries, third-party systems, network calls, and additional functionalities added by the Yellow Team. The Yellow Team may barely be aware of some of the dependencies behind their own code.
- Implement DevSecOps practices
- Perform secure code analysis
- Develop secure coding standards
- Train developers in security practices
- Automate security testing in the development pipeline
People who usually compose this team are developers with security specialization, DevSecOps engineers, application security architects, and SAST/DAST/OWASP specialists.
Orange Team

Red + Yellow = Orange
The Orange Team focuses on threat analysis and intelligence, collecting and processing information about potential adversaries and their tactics.
- Collect and analyze threat intelligence
- Identify emerging trends in cyberattacks
- Develop adversary profiles (threat actors)
- Share relevant information with other teams
- Prioritize threats based on organizational context
The Orange Team is typically composed of threat intelligence specialists, including: CTI (Cyber Threat Intelligence) analysts, security researchers, threat hunting specialists, OSINT (open-source intelligence) professionals, and attack attribution experts. These professionals work to identify, analyze, and contextualize emerging threats, allowing the organization to prepare proactively against possible attacks.
White Team
The White team has a very different and strategic role. While other teams (like Red, Blue, Purple, etc.) are more focused on attacking, defending, or combining both, this team takes care of governance, ethics, education, and security coordination as a whole.
- Education and training
- Define rules of engagement for security exercises
- Monitor exercises to ensure compliance with established parameters and prevent exercises from harming real operations
- Evaluate results impartially
- Document lessons learned
- Governance and compliance policies
- Coordination and facilitation
- Ethics and legitimacy to ensure all actions are within the law
- Ensure all teams are aligned with the organization's security objectives
- Act strongly in audits and frameworks like ISO, NIST, LGPD/GDPR
The White Team acts as referee and coordinator in security exercises, ensuring simulations and tests are conducted ethically and controlledly, ensuring security exercises contribute to the organization's compliance objectives rather than creating additional risks.
Implementation in Organizations
Implementing the Information Security Color Wheel doesn't necessarily require distinct teams for each category. In smaller organizations, a single professional can assume multiple roles as needed. The fundamental is to ensure coverage of all essential functions, even with limited human resources.
Larger organizations have the option to adopt more formal structures, either with exclusive teams for each function or grouping related functions in specific departments.
The Color Wheel represents a flexible and efficient approach to organizing the various organizational security functions. Its adoption allows companies to ensure broad risk coverage, stimulate collaboration among specialists, and foster a resilient and adaptable security culture.
This model is dynamic and constantly evolves to respond to new challenges, reflecting the changing nature of the contemporary cybersecurity threat landscape.